AWS IAM Identity Center (IdC) allows you to manage single sign-on (SSO) access to all your AWS accounts and applications from a single location. We are pleased to announce that Amazon Redshift now integrates with AWS IAM Identity Center, and supports trusted identity propagation, allowing you to use third-party Identity Providers (IdP) such as Microsoft Entra ID (Azure AD), Okta, Ping, and OneLogin. This integration simplifies the authentication and authorization process for Amazon Redshift users using Query Editor V2 or Amazon Quicksight, making it easier for them to securely access your data warehouse. Additionally, this integration positions Amazon Redshift as an IdC-managed application, enabling you to use database role-based access control on your data warehouse for enhanced security.
AWS IAM Identity Center offers automatic user and group provisioning from Okta to itself by utilizing the System for Cross-domain Identity Management (SCIM) 2.0 protocol. This integration allows for seamless synchronization of information between two services, ensuring accurate and up-to-date information in AWS IAM Identity Center.
In this post, we’ll outline a comprehensive guide for setting up SSO to Amazon Redshift using integration with IdC and Okta as the Identity Provider. This guide shows how you can SSO onto Amazon Redshift for Amazon Redshift Query Editor V2 (QEV2).
Solution overview
Using IAM IdC with Amazon Redshift can benefit your organization in the following ways:
- Users can connect to Amazon Redshift without requiring an administrator to set up AWS IAM roles with complex permissions.
- IAM IdC integration allows mapping of IdC groups with Amazon Redshift database roles. Administrators can then assign different privileges to different roles and assigning these roles to different users, giving organizations granular control for user access.
- IdC provides a central location for your users in AWS. You can create users and groups directly in IdC or connect your existing users and groups that you manage in a standards-based identity provider like Okta, Ping Identity, or Microsoft Entra ID (i.e., Azure Active Directory [AD]).
- IdC directs authentication to your chosen source of truth for users and groups, and it maintains a directory of users and groups for access by Amazon Redshift.
- You can share one IdC instance with multiple Amazon Redshift data warehouses with a simple auto-discovery and connect capability. This makes it fast to add clusters without the extra effort of configuring the IdC connection for each, and it ensures that all clusters and workgroups have a consistent view of users, their attributes, and groups. Note: Your organization’s IdC instance must be in the same region as the Amazon Redshift data warehouse you’re connecting to.
- Because user identities are known and logged along with data access, it’s easier for you to meet compliance regulations through auditing user access in AWS CloudTrail authorizes access to data.
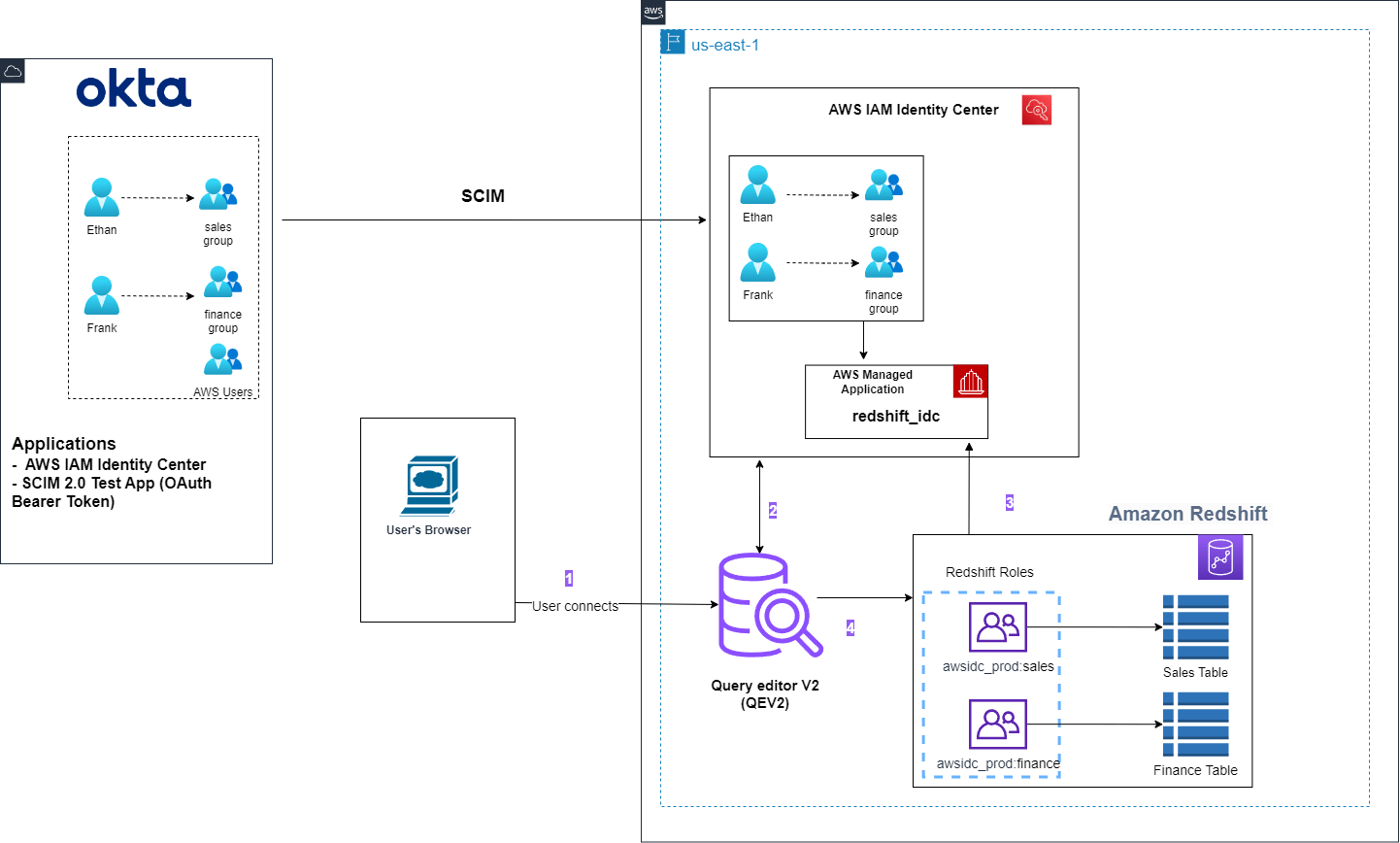
Amazon Redshift Query Editor V2 workflow:
- End user initiates the flow using AWS access portal URL (this URL would be available on IdC dashboard console). A browser pop-up triggers and takes you to the Okta Login page where you enter Okta credentials. After successful authentication, you’ll be logged into the AWS Console as a federated user. Click on your AWS Account and choose the Amazon Redshift Query Editor V2 application. Once you federate to Query Editor V2, select the IdC authentication method.
- QEv2 invokes browser flow where you re-authenticate, this time with their AWS IdC credentials. Since Okta is the IdP, you enter Okta credentials, which are already cached in browser. At this step, federation flow with IdC initiates and at the end of this flow, the Session token and Access token is available to the QEv2 console in browser as cookies.
- Amazon Redshift retrieves your authorization details based on session token retrieved and fetches user’s group membership.
- Upon a successful authentication, you’ll be redirected back to QEV2, but logged in as an IdC authenticated user.
This solution covers following steps:
- Integrate Okta with AWS IdC to sync user and groups.
- Setting up IdC integration with Amazon Redshift
- Assign Users or Groups from IdC to Amazon Redshift Application.
- Enable IdC integration for a new Amazon Redshift provisioned or Amazon Redshift Serverless endpoint.
- Associate an IdC application with an existing provisioned or serverless data warehouse.
- Configure Amazon Redshift role-based access.
- Create a permission set.
- Assign permission set to AWS accounts.
- Federate to Redshift Query Editor V2 using IdC.
- Troubleshooting
Prerequisites
- An AWS account. If you don’t have one, you can sign up for one.
- A Redshift cluster. For setup instructions, see Create a sample Amazon Redshift cluster.
- Alternatively, you could use a Redshift Serverless endpoint. For setup instructions, see Getting started with Amazon Redshift Serverless.
- An Okta account that has an active subscription. You need an administrator role to set up the application on Okta. If you’re new to Okta, then you can sign up for a free trial or sign up for a developer account.
Walkthrough
Integrate Okta with AWS IdC to sync user and groups
Enable group and user provisioning from Okta with AWS IdC by following this documentation here.
If you see issues while syncing users and groups, then refer to this section these considerations for using automatic provisioning.
Setting up IAM IdC integration with Amazon Redshift
Amazon Redshift cluster administrator or Amazon Redshift Serverless administrator must perform steps to configure Redshift as an IdC-enabled application. This enables Amazon Redshift to discover and connect to the IdC automatically to receive sign-in and user directory services.
After this, when the Amazon Redshift administrator creates a cluster or workgroup, they can enable the new data warehouse to use IdC and its identity-management capabilities. The point of enabling Amazon Redshift as an IdC-managed application is so you can control user and group permissions from within the IdC, or from a source third-party identity provider that’s integrated with it.
When your database users sign in to an Amazon Redshift database, for example an analyst or a data scientist, it checks their groups in IdC and these are mapped to roles in Amazon Redshift. In this manner, a group can map to an Amazon Redshift database role that allows read access to a set of tables.
The following steps show how to make Amazon Redshift an AWS-managed application with IdC:
- Select IAM Identity Center connection from Amazon Redshift console menu.
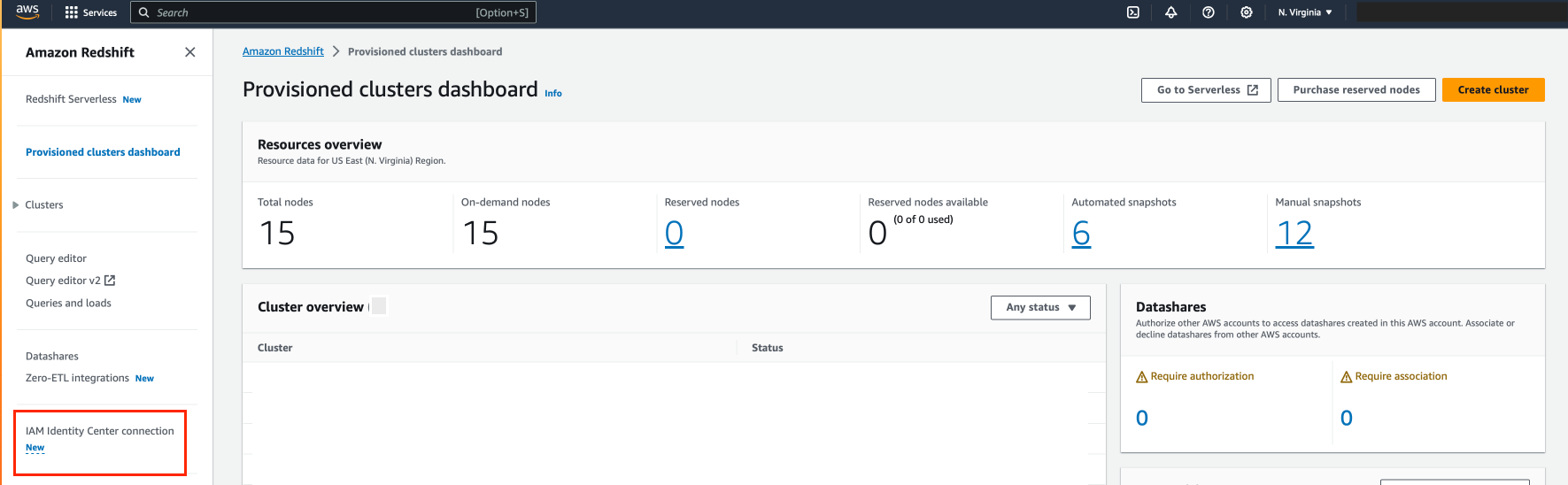
- Choose Create application
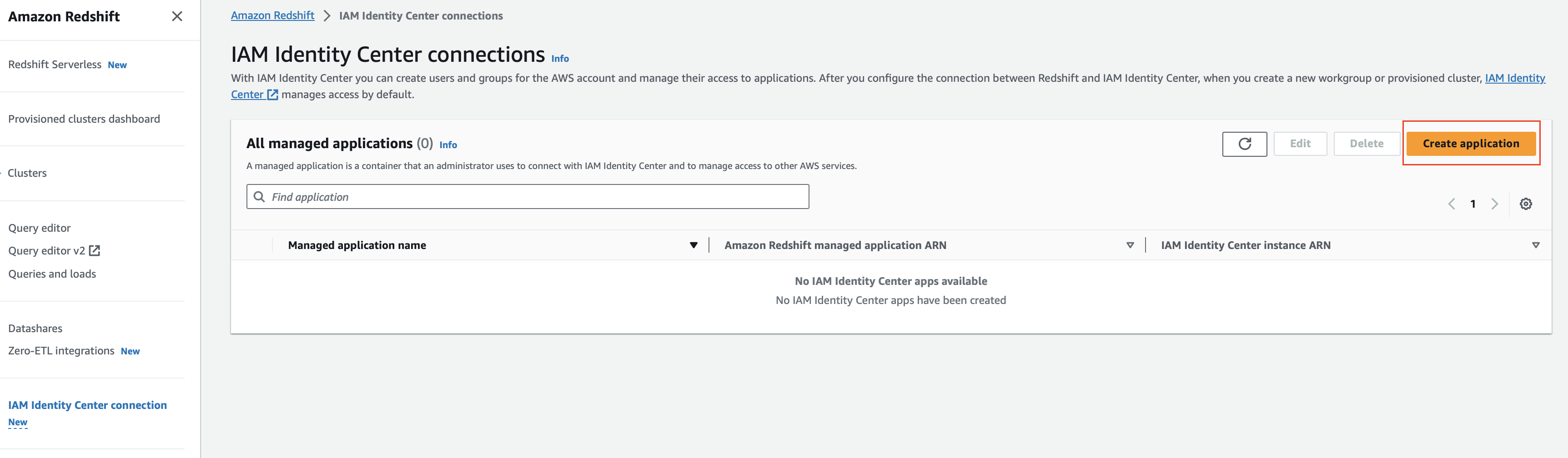
- The IAM Identity Center connection opens. Choose Next.
- In IAM Identity Center integration setup section, for:
- IAM Identity Center display name – Enter a unique name for Amazon Redshift’s IdC-managed application.
- Managed application name – You can enter the managed Amazon Redshift application name or use the assigned value as it is.
- In Connection with third-party identity providers section, for:
- Identity Provider Namespace – Specify the unique namespace for your organization. This is typically an abbreviated version of your organization’s name. It’s added as a prefix for your IdC-managed users and roles in the Amazon Redshift database.
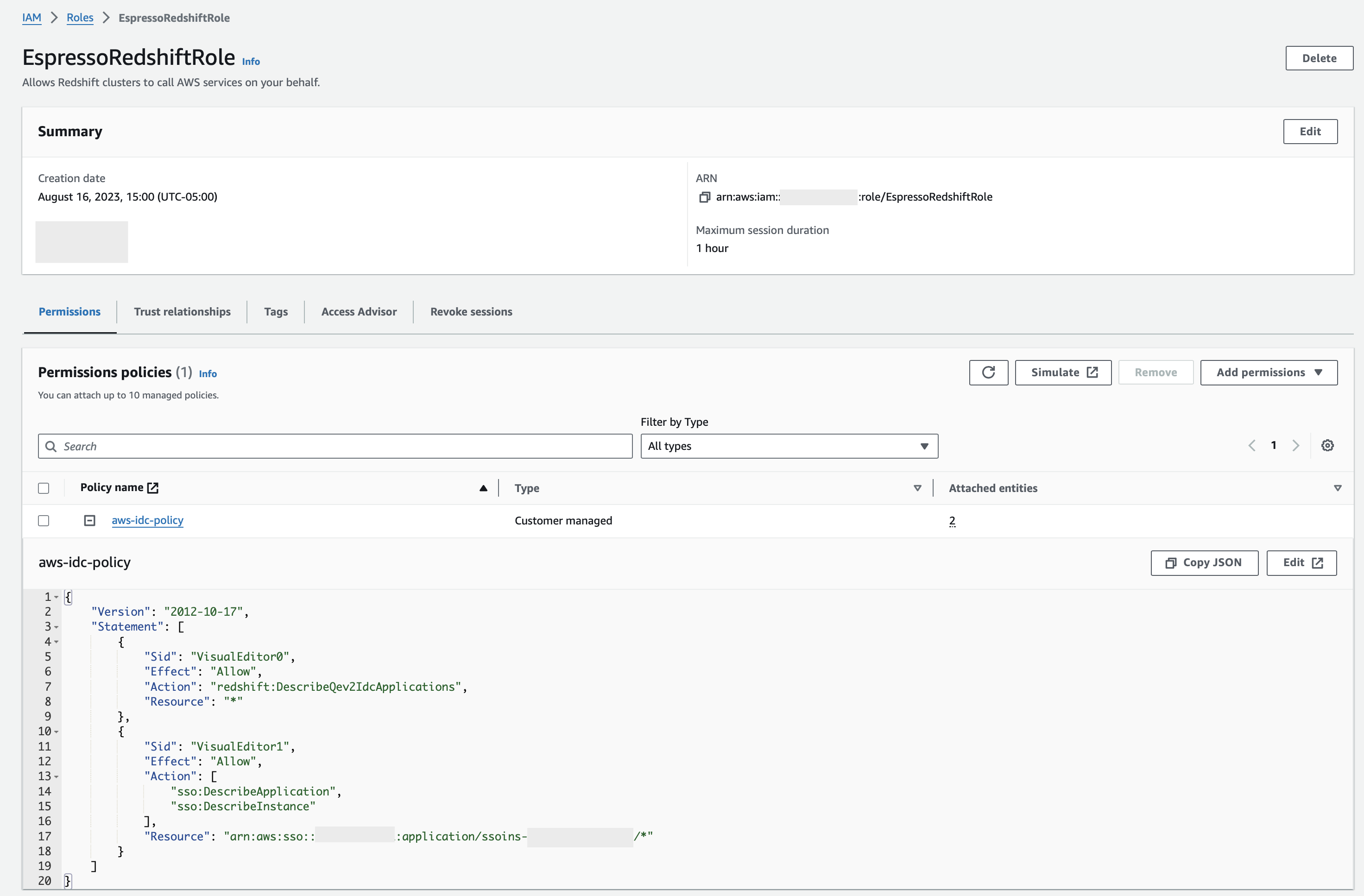
- In IAM role for IAM Identity Center access – Select an IAM role to use. You can create a new IAM role if you don’t have an existing one. The specific policy permissions required are the following:
-
- sso:DescribeApplication – Required to create an identity provider (IdP) entry in the catalog.
- sso:DescribeInstance – Used to manually create IdP federated roles or users.
- redshift:DescribeQev2IdcApplications – Used to detect capability for IDC authentication from Redshift Query Editor V2.
The following screenshot is from the IAM role:
- We won’t enable Trusted identity propagation because we are not integrating with AWS Lake Formation in this post.
- Choose Next.

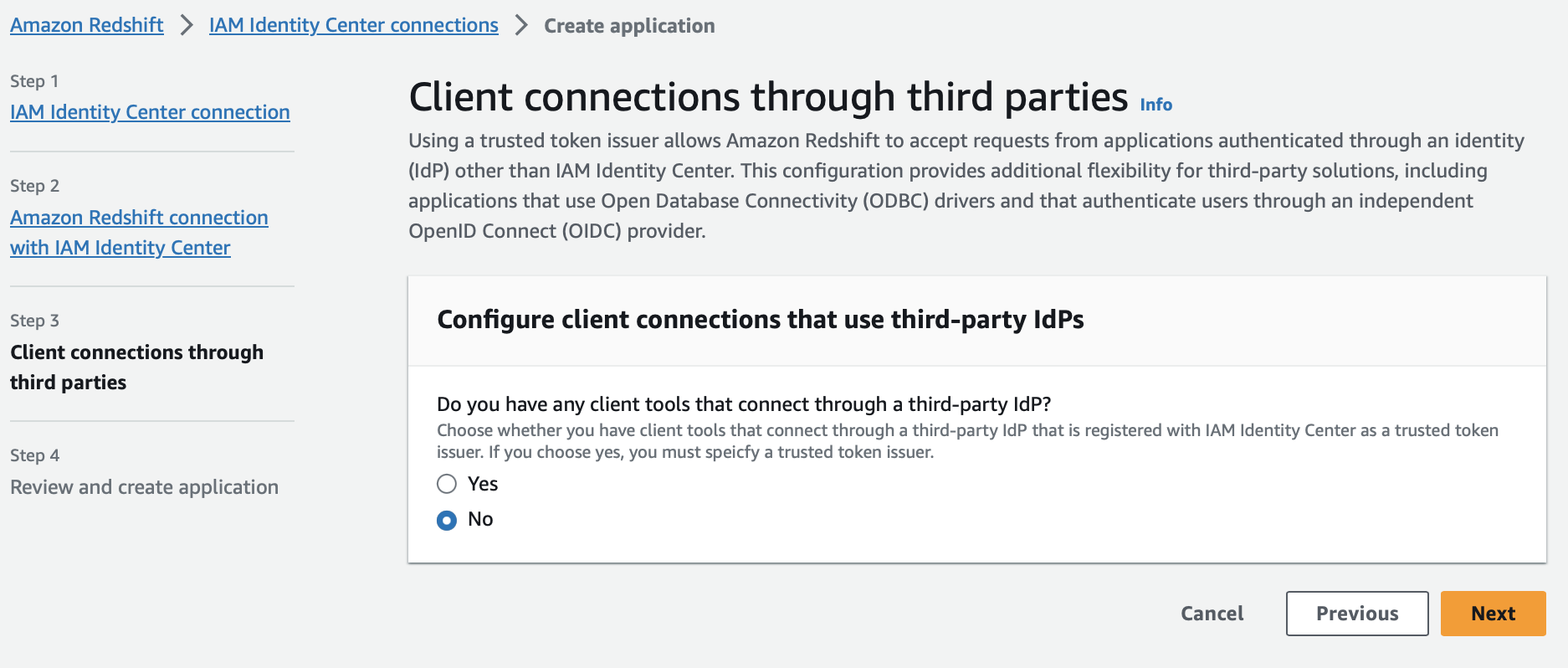
- In Configure client connections that use third-party IdPs section, choose Yes if you want to connect Amazon Redshift with a third-party application. Otherwise, choose No. For this post we chose No because we’ll be integrating only with Amazon Redshift Query Editor V2.
- Choose Next.
- In the Review and create application section, review all the details you have entered before and choose Create application.
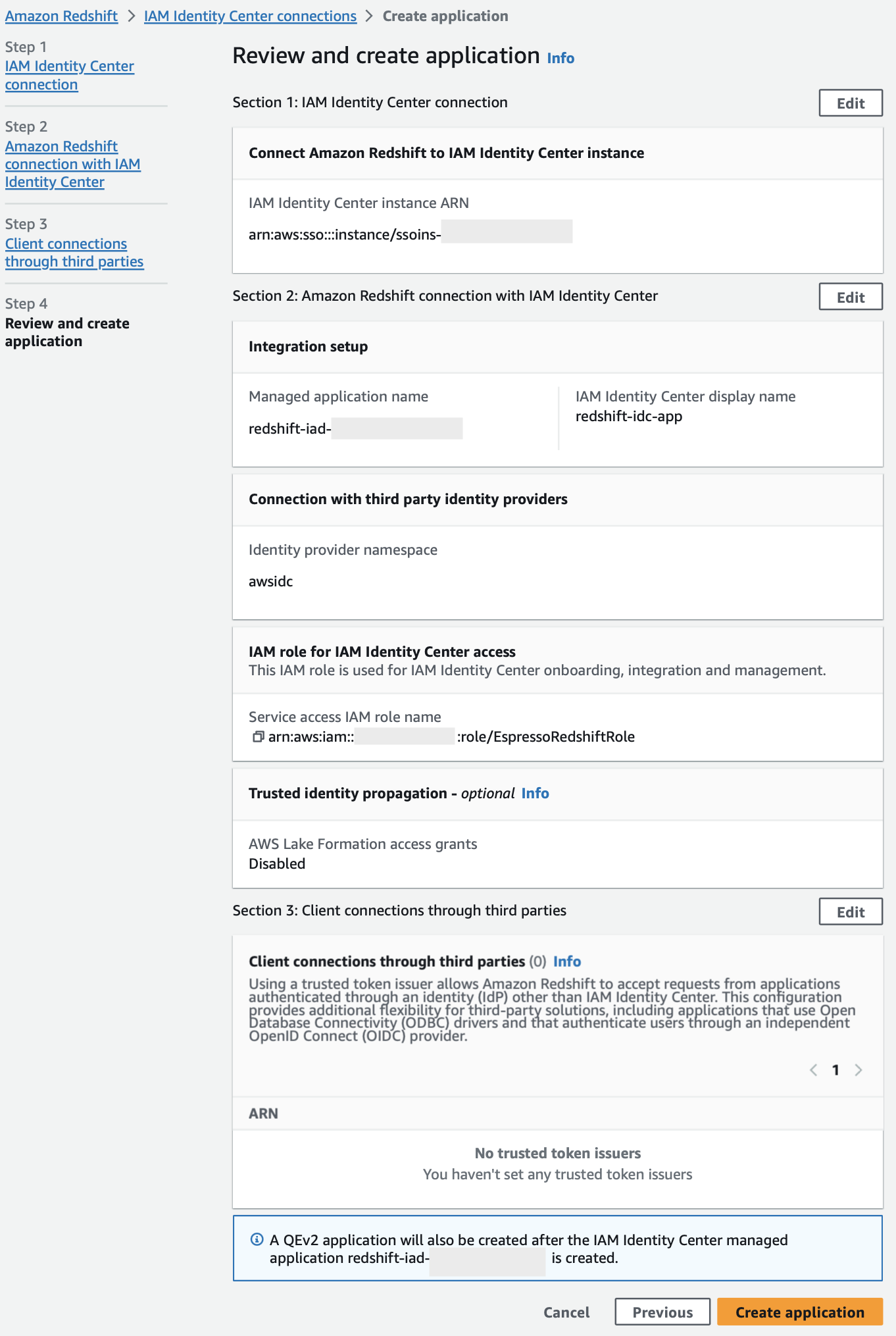
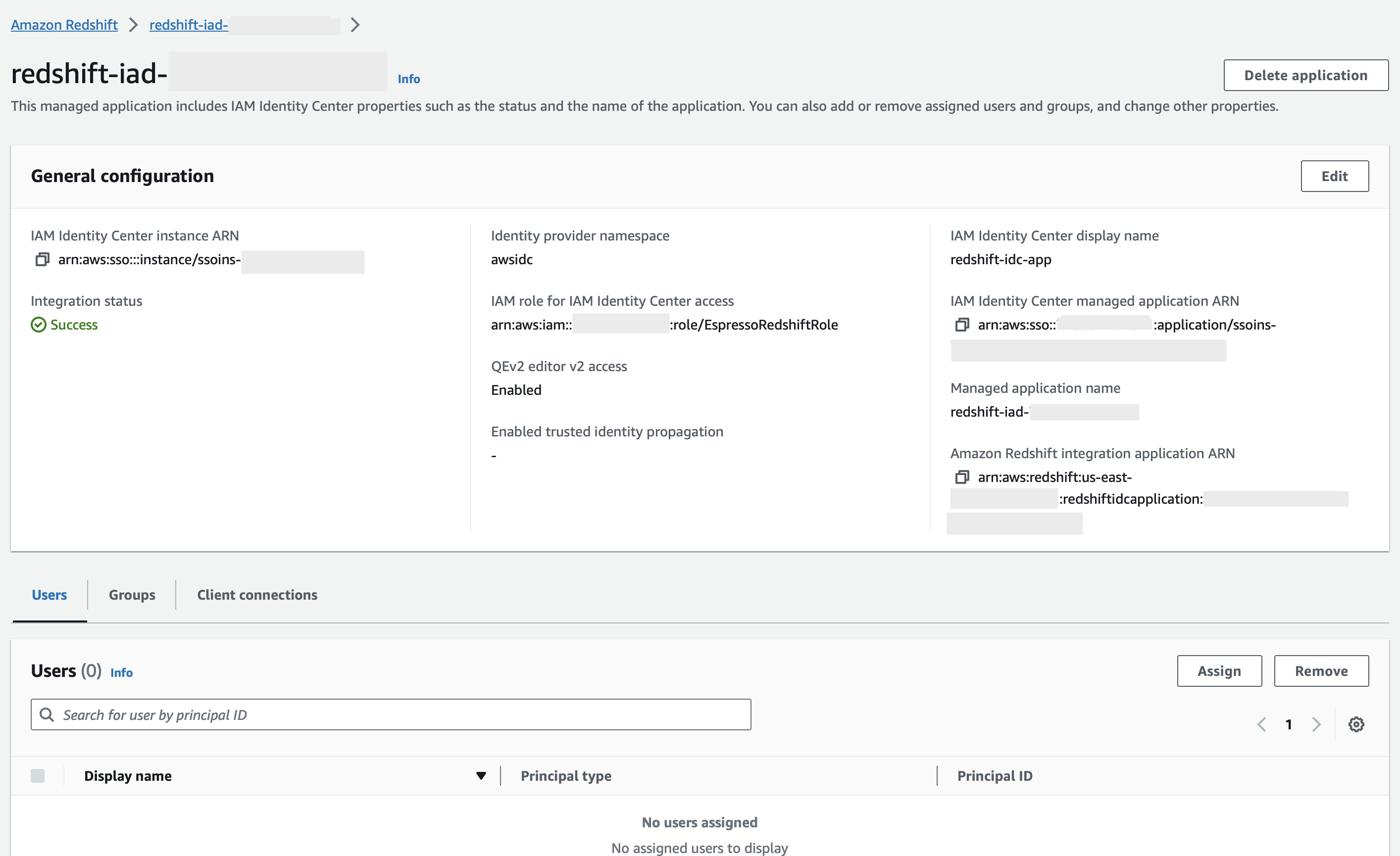
After the Amazon Redshift administrator finishes the steps and saves the configuration, the IdC properties appear in the Redshift Console. Completing these tasks makes Redshift an IdC-enabled application.
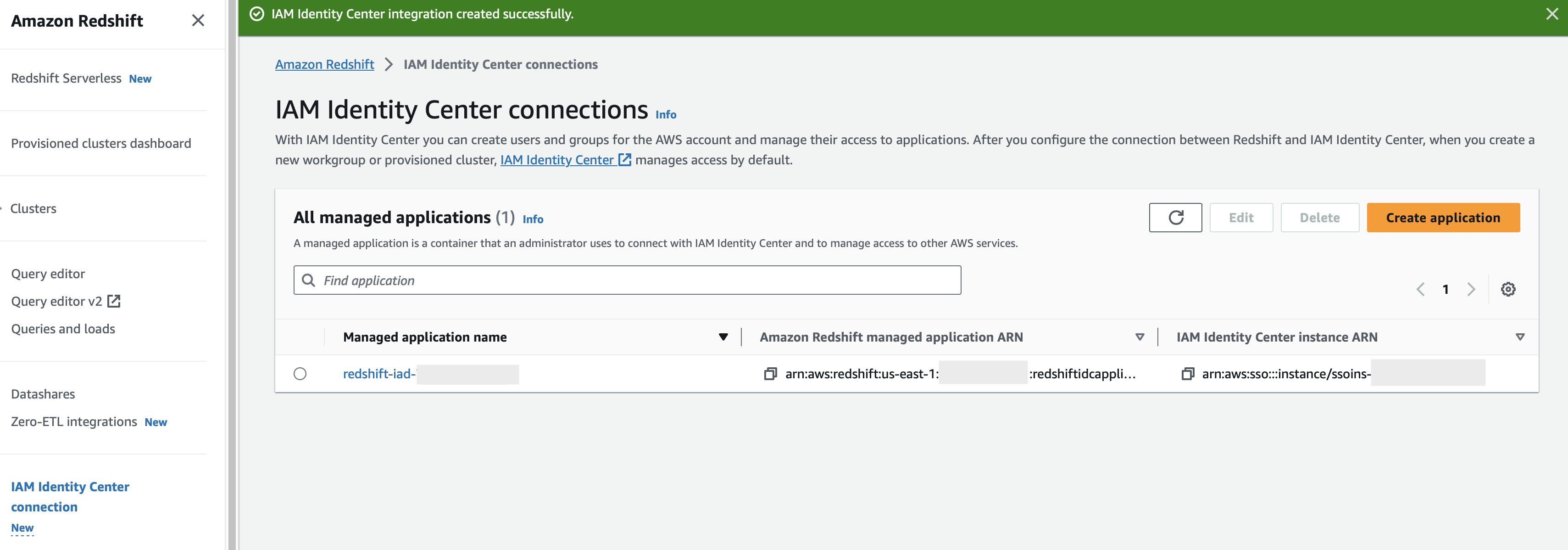
After you select the managed application name, the properties in the console includes the integration status. It says Success when it’s completed. This status indicates if IdC configuration is completed.
Assigning users or groups from IdC to Amazon Redshift application
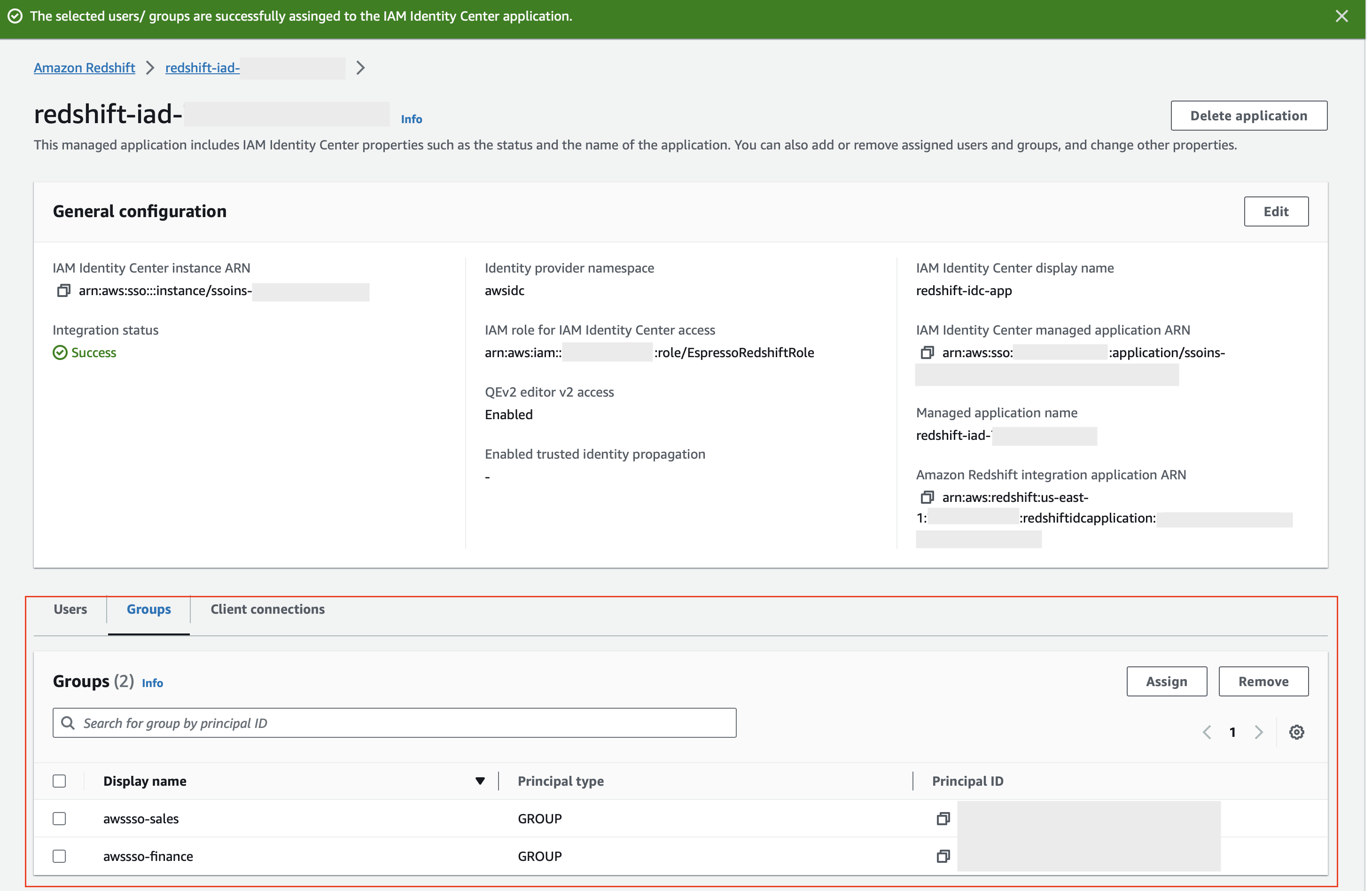
In this step, Users or groups synced to your IdC directory are available to assign to your application where the Amazon Redshift administrator can decide which users or groups from IDC need to be included as part of Amazon Redshift application.
For example, if you have total 20 groups from your IdC and you don’t want all the groups to include as part of Amazon Redshift application, then you have options to choose which IdC groups to include as part of Amazon Redshift-enabled IdC application. Later, you can create two Redshift database roles as part of IDC integration in Amazon Redshift.
The following steps assign groups to Amazon Redshift-enabled IdC application:
- On IAM Identity Center properties in the Amazon Redshift Console, select Assign under Groups tab.
- If this is the first time you’re assigning groups, then you’ll see a notification. Select Get started.
- Enter which groups you want to synchronize in the application. In this example, we chose the groups wssso-sales and awssso-finance.
- Choose Done.
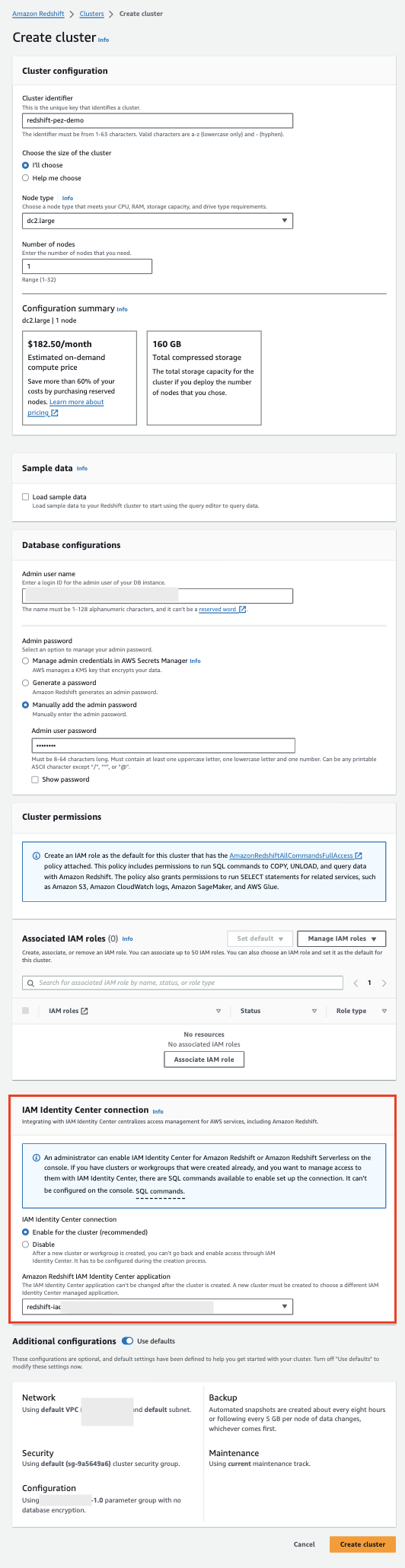
Enabling IdC integration for a new Amazon Redshift provisioned cluster or Amazon Redshift Serverless
After completing steps under section (Setting up IAM Identity Center integration with Amazon Redshift) — Amazon Redshift database administrator needs to configure new Redshift resources to work in alignment with IdC to make sign-in and data access easier. This is performed as part of the steps to create a provisioned cluster or a Serverless workgroup. Anyone with permissions to create Amazon Redshift resources can perform these IdC integration tasks. When you create a provisioned cluster, you start by choosing Create Cluster in the Amazon Redshift Console.
- Choose Enable for the cluster (recommended) in the section for IAM Identity Center connection in the create-cluster steps.
- From the drop down, choose the redshift application which you created in above steps.
Note that when a new data warehouse is created, the IAM role specified for IdC integration is automatically attached to the provisioned cluster or Serverless Namespace. After you finish entering the required cluster metadata and create the resource, you can check the status for IdC integration in the properties.
Associating an IdC application with an existing provisioned cluster or Serverless endpoint
If you have an existing provisioned cluster or serverless workgroup that you would like to enable for IdC integration, then you can do that by running a SQL command. You run the following command to enable integration. It’s required that a database administrator run the query.
Example:
To alter the IdP, use the following command (this new set of parameter values completely replaces the current values):
Few of the examples are:
Note: If you update the idc-namespace value, then all the new cluster created afterwards will be using the updated namespace.
For existing clusters or serverless workgroups, you need to update the namespace manually on each Amazon Redshift cluster using the previous command. Also, all the database roles associated with identity provider will be updated with new namespace value.
You can disable or enable the identity provider using the following command:
Example:
You can drop an existing identity provider. The following example shows how CASCADE deletes users and roles attached to the identity provider.
Configure Amazon Redshift role-based access
In this step, we pre-create the database roles in Amazon Redshift based on the groups that you synced in IdC. Make sure the role name matches with the IdC Group name.
Amazon Redshift roles simplify managing privileges required for your end-users. In this post, we create two database roles, sales and finance, and grant them access to query tables with sales and finance data, respectively. You can download this sample SQL Notebook and import into Redshift Query Editor v2 to run all cells in the notebook used in this example. Alternatively, you can copy and enter the SQL into your SQL client.
Below is the syntax to create role in Amazon Redshift:
For example:
Create the sales and finance database schema:
Creating the tables:
Below is the syntax to grant permission to the Amazon Redshift Serverless role:
Grant relevant permission to the role as per your requirement. In following example, we grant full permission to role sales on sales_schema and only select permission on finance_schema to role finance.
For example:
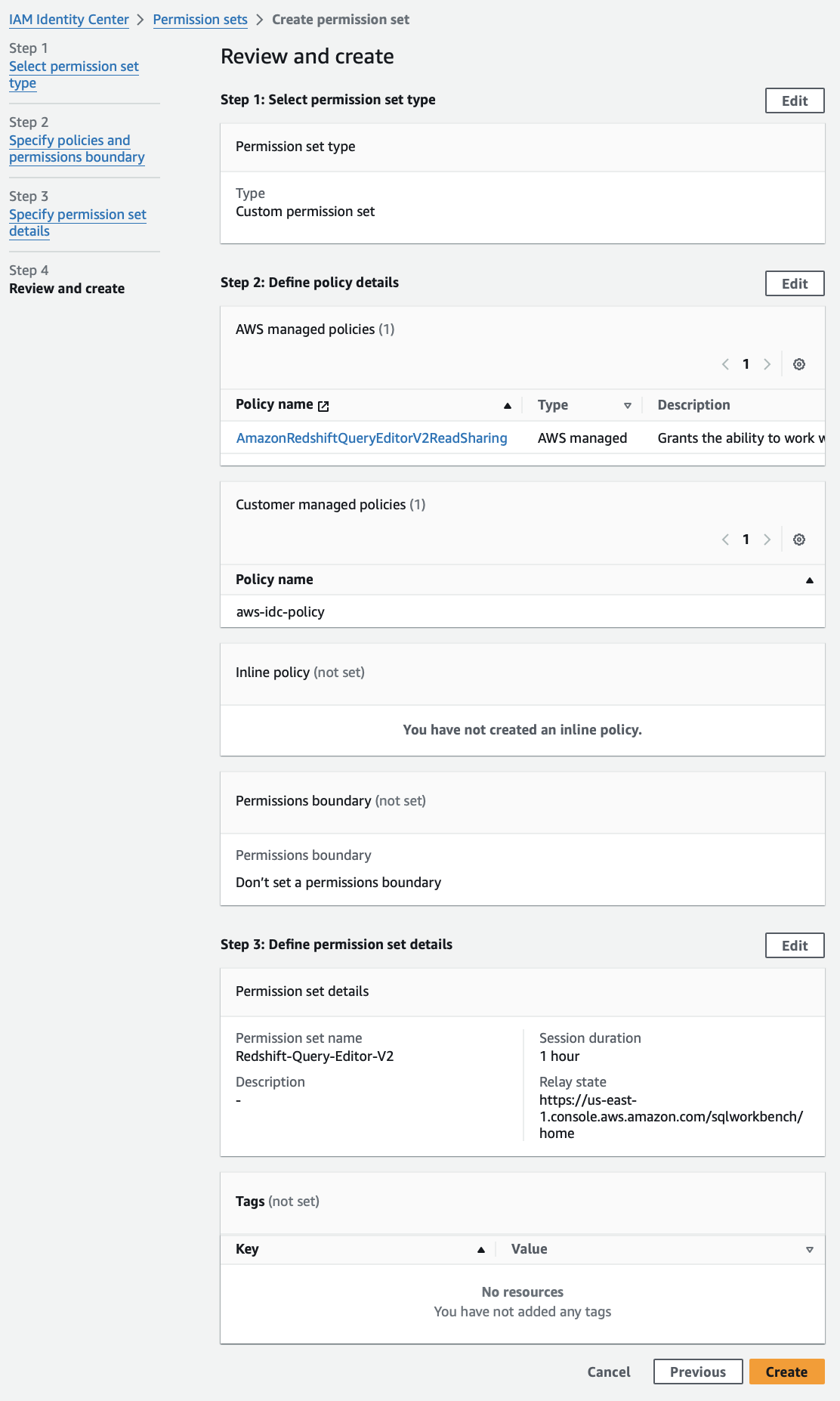
Create a permission set
A permission set is a template that you create and maintain that defines a collection of one or more IAM policies. Permission sets simplify the assignment of AWS account access for users and groups in your organization. We’ll create a permission set to allow federated user to access Query Editor V
The following steps to create permission set:
- Open the IAM Identity Center Console.
- In the navigation pane, under Multi-Account permissions, choose Permission sets.
- Choose Create permission set.

- Choose Custom permission set and then choose Next.
- Under AWS managed policies, choose AmazonRedshiftQueryEditorV2ReadSharing.
- Under Customer managed policies, provide the policy name which you created in step 4 under section – Setting up IAM Identity Center integration with Amazon Redshift.
- Choose Next.
- Enter permission set name. For example, Amazon Redshift-Query-Editor-V2.
- Under Relay state – optional – set default relay state to the Query Editor V2 URL, using the format :
https://<region>.console.aws.amazon.com/sqlworkbench/home.
For this post, we use:https://us-east-1.console.aws.amazon.com/sqlworkbench/home. - Choose Next.
- On the Review and create screen, choose Create. The console displays the following message: The permission set Redshift-Query-Editor-V2 was successfully created.
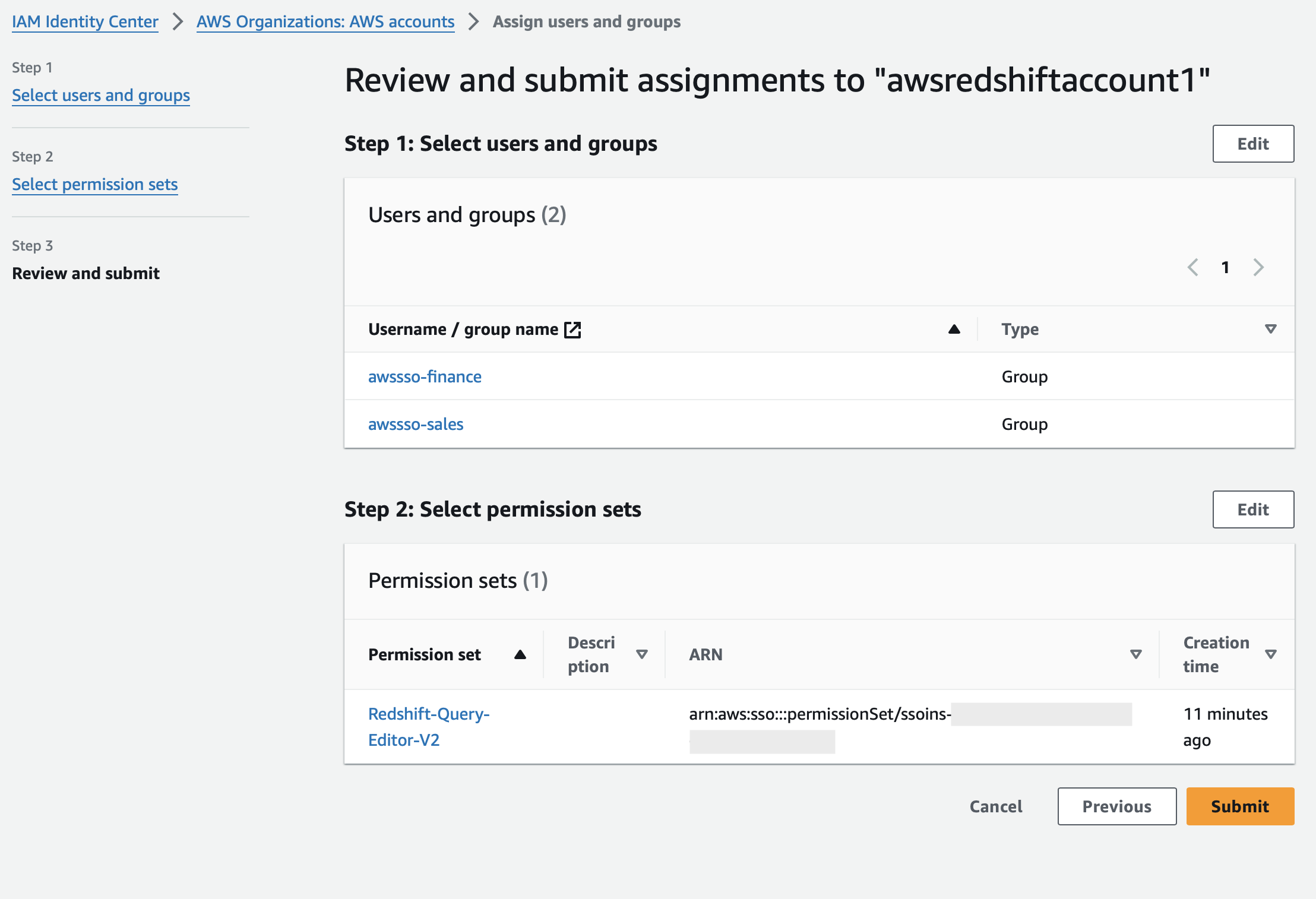
Assign permission set to AWS accounts
- Open the IAM Identity Center Console.
- In the navigation pane, under Multi-account permissions, choose AWS accounts.
- On the AWS accounts page, select one or more AWS accounts that you want to assign single sign-on access to.
- Choose Assign users or groups.
- On the Assign users and groups to AWS-account-name, choose the groups that you want to create the permission set for. Then, choose Next.
- On the Assign permission sets to AWS-account-name, choose the permission set you created in the section – Create a permission set. Then, choose Next.
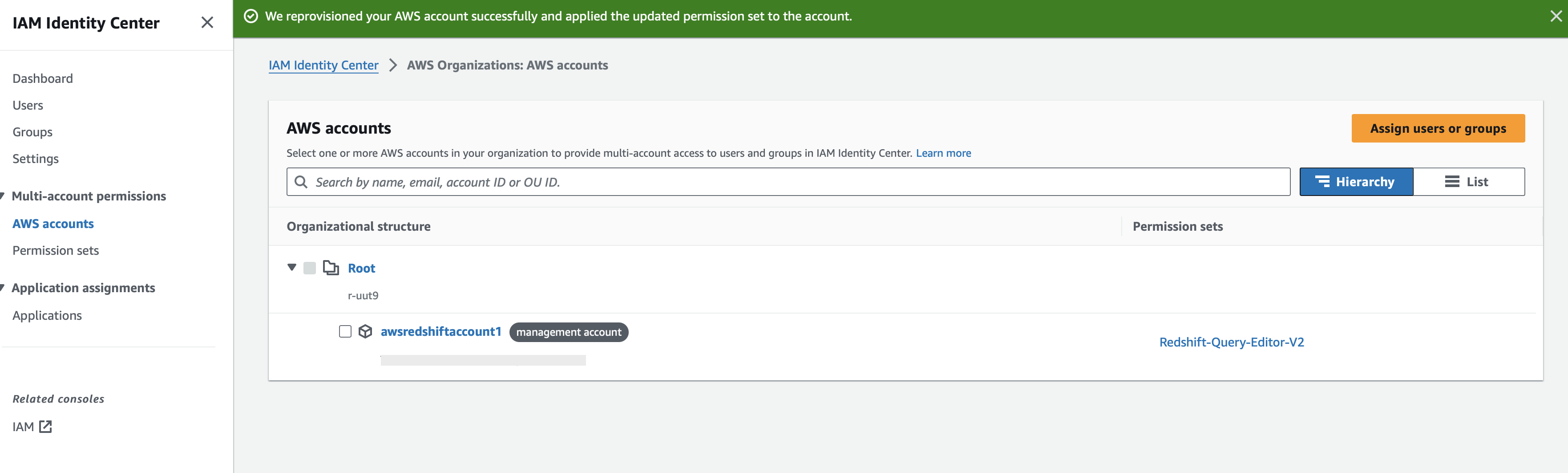
- On the Review and submit assignments to AWS-account-name page, for Review and submit, choose Submit. The console displays the following message: We reprovisioned your AWS account successfully and applied the updated permission set to the account.
Federate to Amazon Redshift using Query Editor V2 using IdC
Now you’re ready to connect to Amazon Redshift Query Editor V2 and federated login using IdC authentication:
- Open the IAM Identity Center Console.
- Go to dashboard and select the AWS access portal URL.
- A browser pop-up triggers and takes you to the Okta Login page where you enter your Okta credentials.
- After successful authentication, you’ll be logged into the AWS console as a federated user.
- Select your AWS Account and choose the Amazon Redshift Query Editor V2 application.
- Once you federate to Query Editor V2, choose your Redshift instance (i.e., right-click) and choose Create connection.
- To authenticate using IdC, choose the authentication method IAM Identity Center.
- It will show a pop-up and since your Okta credentials is already cached, it utilizes the same credentials and connects to Amazon Redshift Query Editor V2 using IdC authentication.
The following demonstration shows a federated user (Ethan) used the AWS access portal URL to access Amazon Redshift using IdC authentication. User Ethan accesses the sales_schema tables. If User Ethan tries to access the tables in finance_schema, then the user gets a permission denied error.
Troubleshooting
- If you get the following error:
This means that you are trying to create a role with a wrong namespace. Please check current namespace using the command select * from identity_providers;
- If you get below error:
This means that an IAM role doesn’t have sufficient privileges to access to the IdC. Your IAM role should contain a policy with following permissions:
- If you get below error:
Please make sure that the user and group are added to the Amazon Redshift IdC application.
Clean up
Complete the following steps to clean up your resources:
- Delete the Okta Applications which you have created to integrate with IdC.
- Delete IAM Identity Center configuration.
- Delete the Redshift application and the Redshift provisioned cluster which you have created for testing.
- Delete the IAM role which you have created for IdC and Redshift integration.
Conclusion
In this post, we showed you a detailed walkthrough of how you can integrate Okta with the IdC and Amazon Redshift Query Editor version 2 to simplify your SSO setup. This integration allows you to use role-based access control with Amazon Redshift. We encourage you to try out this integration.
To learn more about IdC with Amazon Redshift, visit the documentation.
About the Authors
 Debu Panda is a Senior Manager, Product Management at AWS. He is an industry leader in analytics, application platform, and database technologies, and has more than 25 years of experience in the IT world.
Debu Panda is a Senior Manager, Product Management at AWS. He is an industry leader in analytics, application platform, and database technologies, and has more than 25 years of experience in the IT world.
 Maneesh Sharma is a Senior Database Engineer at AWS with more than a decade of experience designing and implementing large-scale data warehouse and analytics solutions. He collaborates with various Amazon Redshift Partners and customers to drive better integration.
Maneesh Sharma is a Senior Database Engineer at AWS with more than a decade of experience designing and implementing large-scale data warehouse and analytics solutions. He collaborates with various Amazon Redshift Partners and customers to drive better integration.
 Harshida Patel is a Principal Solutions Architect, Analytics with AWS.
Harshida Patel is a Principal Solutions Architect, Analytics with AWS.
 Praveen Kumar Ramakrishnan is a Senior Software Engineer at AWS. He has nearly 20 years of experience spanning various domains including filesystems, storage virtualization and network security. At AWS, he focuses on enhancing the Redshift data security.
Praveen Kumar Ramakrishnan is a Senior Software Engineer at AWS. He has nearly 20 years of experience spanning various domains including filesystems, storage virtualization and network security. At AWS, he focuses on enhancing the Redshift data security.
 Karthik Ramanathan is a Sr. Software Engineer with AWS Redshift and is based in San Francisco. He brings close to two decades of development experience across the networking, data storage and IoT verticals prior to Redshift. When not at work, he is also a writer and loves to be in the water.
Karthik Ramanathan is a Sr. Software Engineer with AWS Redshift and is based in San Francisco. He brings close to two decades of development experience across the networking, data storage and IoT verticals prior to Redshift. When not at work, he is also a writer and loves to be in the water.